Note: I’m based in Korea, so some context here is Korea-specific.
1. Introduction
Sealed Secrets is great overall, but it has one annoying issue: every time I configure something, I have to create a Secrets.yaml, convert it to Sealed Secrets via the CLI, and then add it to Git. It’s incredibly tedious.
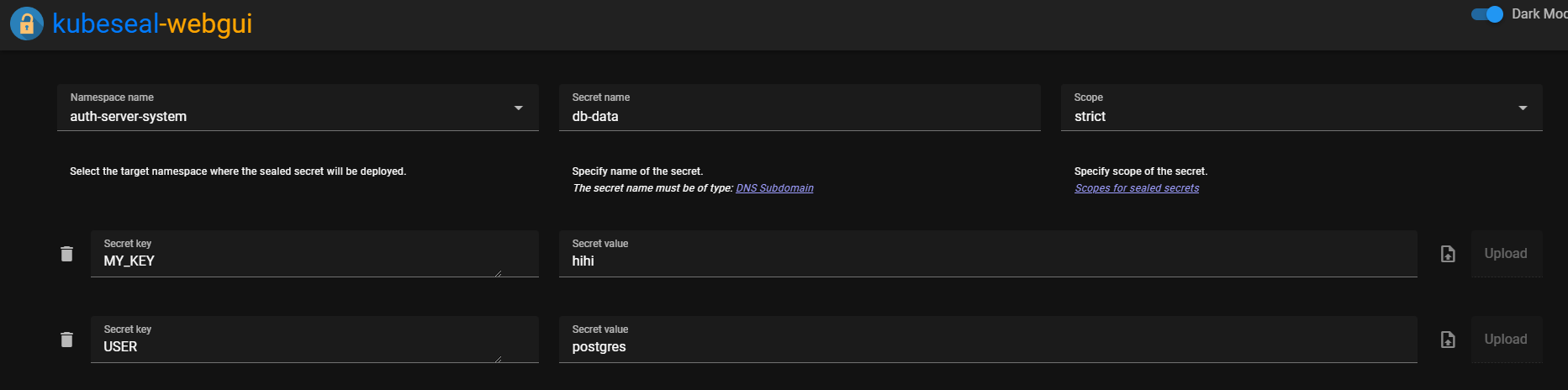
To make this a bit easier, I’m going to build a simple Web UI using kubeseal-webgui .
2. Installation
Let’s install it easily using ArgoCD again!
modules/sealed-secrets-system/kubeseal-webgui.yaml
# https://github.com/Jaydee94/kubeseal-webgui
apiVersion: argoproj.io/v1alpha1
kind: Application
metadata:
name: kubeseal-webgui
namespace: argocd
spec:
destination:
namespace: sealed-secrets-system
server: 'https://kubernetes.default.svc'
source:
repoURL: 'https://jaydee94.github.io/kubeseal-webgui'
targetRevision: 5.1.4
chart: kubeseal-webgui
helm:
parameters:
- name: api.url
value: https://<web ui를 사용할 subdomain 예시:seal.lemon.com>
- name: sealedSecrets.autoFetchCert
value: 'true'
- name: sealedSecrets.controllerName
value: sealed-secrets
- name: sealedSecrets.controllerNamespace
value: sealed-secrets-system
sources: []
project: defaultmodules/sealed-secrets-system/ingress.yaml
apiVersion: traefik.containo.us/v1alpha1
kind: IngressRoute
metadata:
name: sealed-secrets-ingress
namespace: sealed-secrets-system
spec:
tls:
certResolver: le
routes:
- kind: Rule
match: Host(`<web ui를 사용할 subdomain 예시:seal.lemon.com>`)
services:
- name: kubeseal-webgui
port: 8080If needed, add Basic Auth by referring to the previous post .
After that, you can easily create Sealed Secrets through the UI!
Comments